A common challenge for teams integrating Azure Databricks with Microsoft Entra ID (formerly Azure AD) is how to synchronize groups efficiently. While SCIM is typically used for this, there’s now a much simpler way – thanks to a public preview feature that allows you to directly reference Entra ID groupsCzytaj dalej / Read more
The Hidden Cost of Starting Databricks Clusters: How VMs Traffic Can Drain Your Budget
TL;DR: Key Findings Every Databricks cluster node downloads over 12 GiB of data during startup. When routed via Azure Firewall (Data Exfiltration pattern), this can lead to monthly costs exceeding €3,000+ just for control plane traffic. For one bank’s project, this behavior caused over 100 TB of unexpected traffic throughCzytaj dalej / Read more
Variability in Azure Data Factory pipeline run times and how Azure region load affects them?
Azure Data Factory is a powerful tool, offering a vast range of possibilities, though it can be a bit intricate in terms of pricing and architecture. It’s very dear to me, as I appreciate it for many improvements and conveniences compared to its ancestor, SQL Server Integration Services. However, yearsCzytaj dalej / Read more
Understanding the 4-Minute SLA in Azure Data Factory Activities
SLA of the Azure Data Factory service This might be the first time you’re hearing this, but the Azure Data Factory service does NOT GUARANTEE an immediate or even a few seconds’ delay in starting any single activity in your pipelines! In fact, the guarantee for execution time is justCzytaj dalej / Read more
The fastest and cheapest way to transfer data between Storage Accounts in Azure?
My recommendation: azcopy ! And no! You don’t need a machine with fast internet to mediate the transfer. The service allows data transfer through an internal backbone using the storage-to-storage API. My throughput was about 5.6 GB per second (yes, gigabytes, not gigabits)! Of course, there are a few keyCzytaj dalej / Read more
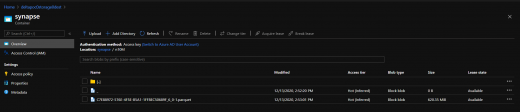
Exporting data to PARQUET file and ADLS Gen2 using Azure Synapse Serverless
Exporting query data is quite simple as one-two-three: One: define your file format
|
1 2 |
CREATE EXTERNAL FILE FORMAT parquetfile1 WITH ( FORMAT_TYPE = PARQUET, DATA_COMPRESSION = 'org.apache.hadoop.io.compress.SnappyCodec' ); |
Two: define your file location (note: you should have read/write/list permission the path)
|
1 2 |
CREATE EXTERNAL DATA SOURCE ADLS_DS WITH( LOCATION = 'abfss://synapse@deltapoc0storage0dest.dfs.core.windows.net') |
Three: Create external table in particular location, using format and path from previous steps:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
CREATE EXTERNAL TABLE dbo.n10M WITH ( LOCATION = '/n10M', DATA_SOURCE = ADLS_DS, FILE_FORMAT = parquetfile1 ) AS WITH lv0 AS (SELECT 0 g UNION ALL SELECT 0) ,lv1 AS (SELECT 0 g FROM lv0 a CROSS JOIN lv0 b) -- 4 ,lv2 AS (SELECT 0 g FROM lv1 a CROSS JOIN lv1 b) -- 16 ,lv3 AS (SELECT 0 g FROM lv2 a CROSS JOIN lv2 b) -- 256 ,lv4 AS (SELECT 0 g FROM lv3 a CROSS JOIN lv3 b) -- 65,536 ,lv5 AS (SELECT 0 g FROM lv4 a CROSS JOIN lv4 b) -- 4,294,967,296 ,Tally (n) AS (SELECT ROW_NUMBER() OVER (ORDER BY (SELECT NULL)) FROM lv5) SELECT TOP (10000000) n1=n, n2=n, n3=n, n4=n, n5=n, n6=n, n7=n, n8=n, n9=n, n10=n FROM Tally |
Took 43sec toCzytaj dalej / Read more
Azure Active Directory – inviting users when you are not an AAD admin
By default, all users, including guests, can invite guest users. Isn’t it beautiful? No, it’s not! Definitely not if you are an AAD admin. So treat this post as a warning. Your users, including !!guest users!! can invite other users to your AAD by default. If you are ok withCzytaj dalej / Read more
Worth watching! EightKB – SQL Server Internals Conference 17.06.2020
Most of the lectures at conferences focus on general topics, often at a basic level to introduce the listener to a certain area, just to interest him. And there are only a few that I come out with a head full of detailed technical knowledge, very useful in understanding theCzytaj dalej / Read more
Are you looking for a Client ID but actually you don’t have permission to access Azure Active Directory?
That was my case. And to be honest it wasn’t easy to find the solution, although the solution is pretty easy 😉 All pages that I visited are describing on how to do it but using only Active Directory within the portal… The truth is, that even if you can’tCzytaj dalej / Read more
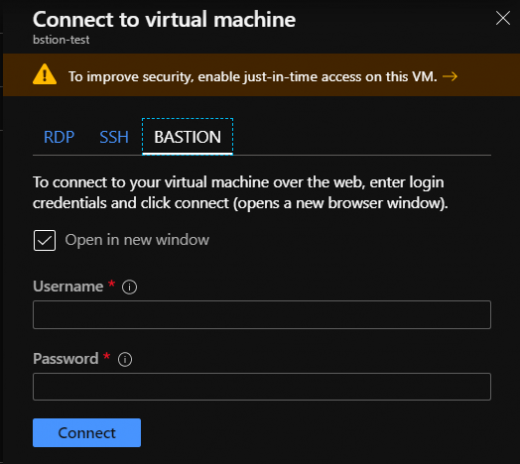
Azure Bastion – creating proper NSG rules
Just in case someone came across a problem defining proper nsg rules for Azure Bastion… Well, here they are: Works like a charm 😀 And below the ARM for it:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 |
{ "$schema": "https://schema.management.azure.com/schemas/2019-04-01/deploymentTemplate.json#", "contentVersion": "1.0.0.0", "parameters": { "projectPrefix": { "type": "string", "metadata": { "description": "Prefix for the name of resources." } }, "resourceLocation": { "type": "string", "defaultValue": "[resourceGroup().location]", "metadata": { "description": "Location for all resources." } } }, "variables": { "nsgName": "[concat(parameters('projectPrefix'), 'NSG-Bastion')]" }, "resources": [ { "type": "Microsoft.Network/networkSecurityGroups", "apiVersion": "2019-09-01", "name": "[variables('nsgName')]", "location": "[parameters('resourceLocation')]", "properties": { "securityRules": [ { "name": "InboundFromAny", "properties": { "description": "Allow connection from any host on https.", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "443", "sourceAddressPrefix": "*", "destinationAddressPrefix": "*", "access": "Allow", "priority": 100, "direction": "Inbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "name": "InboundFromGM", "properties": { "description": "This enables the control plane, that is, Gateway Manager to be able to talk to Azure Bastion.", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "443", "sourceAddressPrefix": "GatewayManager", "destinationAddressPrefix": "*", "access": "Allow", "priority": 120, "direction": "Inbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "name": "OutboundToVNET_SSH", "properties": { "description": "Egress Traffic to target VMs: Azure Bastion will reach the target VMs over private IP and SSH port", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "22", "sourceAddressPrefix": "*", "destinationAddressPrefix": "VirtualNetwork", "access": "Allow", "priority": 120, "direction": "Outbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "name": "OutboundToVNET_RDP", "properties": { "description": "Egress Traffic to target VMs: Azure Bastion will reach the target VMs over private IP and RDP port", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "3389", "sourceAddressPrefix": "*", "destinationAddressPrefix": "VirtualNetwork", "access": "Allow", "priority": 110, "direction": "Outbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "name": "OutboundHTTPStoAzureCloud", "properties": { "description": "Egress Traffic to other public endpoints in Azure", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "443", "sourceAddressPrefix": "*", "destinationAddressPrefix": "AzureCloud", "access": "Allow", "priority": 100, "direction": "Outbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } } ] } }, { "type": "Microsoft.Network/networkSecurityGroups/securityRules", "apiVersion": "2019-09-01", "name": "[concat(variables('nsgName'), '/InboundFromAny')]", "dependsOn": [ "[resourceId('Microsoft.Network/networkSecurityGroups', variables('nsgName'))]" ], "properties": { "description": "Allow connection from any host on https.", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "443", "sourceAddressPrefix": "*", "destinationAddressPrefix": "*", "access": "Allow", "priority": 100, "direction": "Inbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "type": "Microsoft.Network/networkSecurityGroups/securityRules", "apiVersion": "2019-09-01", "name": "[concat(variables('nsgName'), '/InboundFromGM')]", "dependsOn": [ "[resourceId('Microsoft.Network/networkSecurityGroups', variables('nsgName'))]" ], "properties": { "description": "This enables the control plane, that is, Gateway Manager to be able to talk to Azure Bastion.", "protocol": "TCP", "sourcePortRange": "*", "sourceAddressPrefix": "GatewayManager", "destinationAddressPrefix": "*", "access": "Allow", "priority": 120, "direction": "Inbound", "sourcePortRanges": [ ], "destinationPortRanges": [ "443", "4443" ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "type": "Microsoft.Network/networkSecurityGroups/securityRules", "apiVersion": "2019-09-01", "name": "[concat(variables('nsgName'), '/OutboundHTTPStoAzureCloud')]", "dependsOn": [ "[resourceId('Microsoft.Network/networkSecurityGroups', variables('nsgName'))]" ], "properties": { "description": "Egress Traffic to other public endpoints in Azure", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "443", "sourceAddressPrefix": "*", "destinationAddressPrefix": "AzureCloud", "access": "Allow", "priority": 100, "direction": "Outbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "type": "Microsoft.Network/networkSecurityGroups/securityRules", "apiVersion": "2019-09-01", "name": "[concat(variables('nsgName'), '/OutboundToVNET_RDP')]", "dependsOn": [ "[resourceId('Microsoft.Network/networkSecurityGroups', variables('nsgName'))]" ], "properties": { "description": "Egress Traffic to target VMs: Azure Bastion will reach the target VMs over private IP and RDP port", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "3389", "sourceAddressPrefix": "*", "destinationAddressPrefix": "VirtualNetwork", "access": "Allow", "priority": 110, "direction": "Outbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } }, { "type": "Microsoft.Network/networkSecurityGroups/securityRules", "apiVersion": "2019-09-01", "name": "[concat(variables('nsgName'), '/OutboundToVNET_SSH')]", "dependsOn": [ "[resourceId('Microsoft.Network/networkSecurityGroups', variables('nsgName'))]" ], "properties": { "description": "Egress Traffic to target VMs: Azure Bastion will reach the target VMs over private IP and SSH port", "protocol": "TCP", "sourcePortRange": "*", "destinationPortRange": "22", "sourceAddressPrefix": "*", "destinationAddressPrefix": "VirtualNetwork", "access": "Allow", "priority": 120, "direction": "Outbound", "sourcePortRanges": [ ], "destinationPortRanges": [ ], "sourceAddressPrefixes": [ ], "destinationAddressPrefixes": [ ] } } ] } |